



Photos by Richard Sanderson | Photos by Kathleen Charters
Since the February General Meeting subject was Home Networking, most items on the table – the two laptops, the projector, the surge protector, the AirPort Extreme, the hard disk – were connected together by the end of the presentation. Three exceptions: the USB microphone, the bottle of water, and the lunch donation tin, though given time the USB microphone would have been easy and the tin only slightly less so. Photo by Richard Sanderson.
Macs were the first personal computers to come with built-in networking. Nothing else needed to be added except cables and connectors, starting with the original 128K Macintosh in 1984.
Yet networking questions continue to be some of the most oft-repeated at Pi meetings. So, for February, the General Meeting was devoted to home networking, and the topic attracted a capacity crowd. Were it not for bodily needs (lunch, restrooms) and deadlines (we had to vacate the building), a large part of the audience seemed content to ask networking questions throughout the afternoon and into the evening. But before the networking questions there was the –
Q: I have an Intel-based iMac and my built-in Webcam does not work.
A. Does not work with what?
Q1a: Does not work with Windows under Parallels.
A. Aha! First, your built-in camera is an iSight camera, not specifically
a Webcam. A Webcam is a camera that transmits images over the Web. The iSight
camera built-in to an iMac is not so limited: it can transmit images to your
desktop, to your grandmother, to Space Shuttles in orbit, to the Web, and
almost anywhere else you can figure out to send images.
The Mac OS X operating system is designed to look for an iSight camera and, if it finds one, it knows that an iSight camera can be used with PhotoBooth and hundreds of other applications. But Windows XP (making a guess that XP is the flavor under discussion) has never heard of an iSight camera, or any other kind of digital camera. Windows XP was released in October 2001; its main purpose was to not be as bad as Windows NT, Windows 2000, and Windows Me, all of which were replaced by Windows XP.
More significantly, Windows XP doesn’t realize it is running on a Mac, doesn’t realize that it is running as a task under Mac OS X, and is generally clueless about most of the universe not made by Microsoft. This is a Good Thing, as otherwise Windows tends to get in trouble.
Drivers for the iSight are included with Apple’s Boot Camp software, but getting these drivers to work with Fusion or Parallels and Windows XP is a non-trivial task.
Q: Apple Mail on my Mac keeps asking for the password every three
or four minutes. This is a new development.
A.: There are two common reasons for this. On slower connections, mostly
dial-up connections or very slow DSL connections, your ISP (Internet Service
Provider) may pass on network packets that convince the mail server you’ve
hung up, so when you ask to get or send mail, the server prompts you for
your password again.
Another common cause, however, are keychain issues. Keychain is a service in Mac OS X that handles password management (it can also do other things, such as store secure notes on the secret location of Atlantis; see Figure 1). If you’ve told Apple Mail to store your password, for example, so you don’t have to type it every time you want to read your E-mail, Keychain does the actual work, not Mail. If you’ve changed your password, or something else has changed (“something else” can range from the mundane to the genuinely obscure), you may need to use Keychain Access (in your Applications/Utilities directory) to reconcile any differences. Keychain Access also includes a function, Keychain First Aid, which will verify that your Keychain is happy and healthy, or repair it if it finds problems.
Figure 1: Keychain Access is used to store passwords, certificates passed back and forth by various applications, and even notes that you want to keep secret. Whatever you do, don’t type this address into Google Earth; it’s a secret.
Q: I downloaded something from Apple called Keychain First Aid (or
a shareware program called Keychain Repair, or…) Can I use
this to fix my Keychain?
A: Please throw it away. It is an old, old utility, and should only be used
with Mac OS X 10.1 and 10.2, and you shouldn’t be
using either in 2009. Use Apple’s supplied Keychain Access utility.
Q.: If I’ve had Mail open for a while, sometimes I’m
prompted for my password again when I try to send mail. Quitting Mail and
opening it again fixes the problem.
A.: This is really the same problem as having a slow connection: the connection
to the mail server has been closed. An easier solution is to simply Get mail,
which will wake up the connection, and then you can send mail; you shouldn’t
need to quit.
Q.: What do I do if I’ve forgotten my Pi mail password?
A.: Your wap.org mail password is the same as your TCS login password, and
vice versa. If you’ve forgotten the password, you can go to http://tcs.wap.org/,
find the “I’ve lost my password” link, and you’ll
be prompted for your member name and membership ID number. The Pi will then
E-mail you a new password to whatever E-mail account you have on file. Naturally,
if you’ve dropped your old mail provider and failed to inform the Pi,
this process will not work…
Q.: My mail download stops before getting all my messages. Why?
A.: There are two common issues. One is all the mail does download,
but since your scroll bar is not updated, you don’t realize all the
mail has downloaded until the next time you launch mail and think: Where
did all this mail come from?
The other common problem is a slow network. This is most common with cable TV companies that also serve as ISPs. Some mail comes in, slowly, and then stops. Because of the slow connection, or the busy mail server, the mail server has simply dropped the connection to you and moved on to someone else. There isn’t much you can do about this except, perhaps, find a different ISP.
You may also run into this issue if someone has sent you an exceptionally large attachment, such as a large photo, or a video file, or (if you are a bureaucrat), an unnecessarily large and obtuse PowerPoint slide set. The large file takes so long to download that the mail server decides you aren’t really paying attention and moves on to someone else. In some cases, repeated attempts to Get your mail will fail because the large file acts as a digital intestinal blockage, with all the predictable painful side effects.
Q.: I have a Web mail account, and I’d like to convert it to a regular
mail account so I can systematize it and arrange things in a more orderly
fashion. Should I use Apple Mail or something like Mozilla’s Thunderbird?
A.: Thunderbird and Apple Mail are very comparable. Both
have spell checking, both allow you to send richly formatted messages, both
will talk to virtually every mail server on the planet, both have excellent
junk mail filtering.
If your employer doesn’t require you to use something like Thunderbird (which
works identically on a Mac or Windows machine), Apple Mail has
some advantages. It works perfectly with Address Book (Thunderbird doesn’t),
it can display embedded TIFF and PDF documents (Thunderbird can’t),
it can sync with Apple’s MobileMe services, and – a not insignificant
point – it is well known to millions of Mac users who can provide aid
and assistance.
But for most common functions, Apple Mail and Thunderbird are
very robust, highly regarded equivalent mail clients.
Q.: Can you use either [Apple Mail or Thunderbird] to automatically
sort messages?
A.: Absolutely. Both mail clients have user-configurable rules or filters
for sorting incoming messages into particular folders.
Q.: Mail has a preference for how often it checks for new mail.
If I’m on a slow connection, should I set it to check more often?
A.: Setting it to check more often can actually slow things down on a slow
connection. In fact, setting a longer period between mail checks might make
your network connection seem faster, since your computer, and network, spend
less time looking for mail. If you are a graphic artist or someone else who
routinely receives very large files, increasing the time interval for checking
mail may be a good idea. But generally speaking, most people will be happy
with the interval set between 10 and 30 minutes.
Q.: I’m trying to get things out of Microsoft Outlook, mostly
addresses, into Apple Mail. Is there an easy way to do this?
A.: Versiontracker (http://www.versiontracker.com/) should have some utilities
that allow you to import information from Outlook into Apple Mail.
If you have Microsoft Office 2004 or Office 2008, Entourage,
Microsoft’s mail tool, can sometimes act as a bridge between Outlook and
Apple Mail, though some pain and suffering will be required.
Q.: I am on Cox (cable Internet service) and sometimes I get a broken icon
in E-mail that is supposed to be a photo. I’m using Safari as
my E-mail client.
A.: Safari is a Web browser, not an E-mail client, so in essence
you are using Web mail to read your mail. If you get a broken icon in these
cases that is supposed to be a photo, it means that the photo was not sent
with the message.
This frequently happens when people forward messages with photos. The photo
was downloaded to the sender’s machine, and they forwarded the message
on to you – but the message you receive points back to the sender’s
computer, which you can’t see. The photo was never attached to the
message.
You may also get a broken icon if your mail client can’t display the image, for some reason. But the image should still show up as an attachment, which you can then save to disk and, presumably, see. If there is no attachment, and you have an icon indicating something is missing, then – the item was not sent, despite the protestations of the sender.
Bob Jarecke asked how many people received the printed Journal, and many raised their hand. When he asked how many had downloaded the electronic version of the Journal, even more responded, which is gratifying.
Bob talked about the electronic Journal a bit, mentioning that it came with an embedded video. This seemed to surprise many, who didn’t realize the image was a video and not a photo.
Bob also put in a plug for Clubhouse Saturdays (http://www.wap.org/events/clubhousesaturday.html)
as a way to both better use the Pi Clubhouse as well as get a chance to talk
one-on-one with other members and Mac owners.
Finally, Bob asked for members to strongly consider running for a position
on the Washington Apple Pi Board of Directors. The Pi can’t exist as
an organization without Board members actively guiding and managing the group,
and the burdens are modest.
As for the coffee break — a regularly scheduled event to get folks up out of their chair and socialize — it was again a beehive of activity. The five dozen donuts were outnumbered by audience members and didn't stand a chance as they all but disappeared in seconds. And, the feeding frenzy didn’t stop there as some folks discovered the lunch break drinks and desert snacks and some of these were gobbled up too. It was a premonition of what was to come, as during the lunch break, the dozen large pizzas ordered vanished in a flash. It was obvious this group was hungry for more than information about home networking.
The Macintosh was the first computer to include networking right out of the box, and this ability has been in the Mac from the start. In 1984, the very first Macintosh supported AppleTalk, and it was an immediate hit with schools, small business, scientific agencies, creative businesses (particularly advertising and print media) and home users.
The Macintosh was also the first personal computer to come with Ethernet as a standard part of the computer, and the first to support Internet protocols as a standard part of the operating system. These innovations allowed Macs to expand beyond the home office or campus network out to the rest of the planet.
Yet networking continues to trip up Mac users, in part because there are no tangible artifacts. When you move groceries from your car to your kitchen, you can see the objects being moved, and measure your progress by the number of bags that leave the car and end up in the kitchen. Networking, however, occurs at an electronic level, out of sight to human eyes. Those that understand networking have frequently been referred to as magicians or wizards since the entire process seems magical. Or, worse, the process seems scientific and technical.
The demonstration part of the meeting started with a bunch of equipment, none of it connected. The equipment:
In the local area, you should not plug your computer into a surge protector but, rather, a UPS (uninterruptible power supply). A UPS insulates your computer from power surges and drops, and power outages, as well as most of the damage you’d expect from a thunderstorm. Surge protectors only protect you from specific types of surges – not from excessive power, and not from the massive surges caused by nearby lightening strikes. Step Number One in setting up a network should be getting a UPS adequate to power your computer and monitor, with enough reserve power left over for the network router or switch.
Q.: Should you plug your printer into the UPS?
A.: Never. And if it is a laser printer, ideally the laser printer should be on a different circuit entirely from your computer. Laser printers tend to create peaks and valleys on the circuit since they use a whole bunch of electricity at once, followed by not much. These surges are anathema to computers.
Q.: How about an inkjet printer.
A.: They should not be plugged into the UPS, either. While they don’t use nearly as much power, you aren’t going to be printing anything if the power is out, so – plug them into something else.
After plugging both computers and the router into the surge protector, there was a short discussion of network speed. Virtually every Mac sold in the 21st century has gigabit Ethernet networking (i.e., very fast networking), so if you need to buy a network switch, get a gigabit switch; they are very inexpensive. The current AirPort Extreme routers and all Time Capsules come with a built-in gigabit switch.
All currently sold Apple laptops have 802.11n wireless networking, the fastest wireless networking available. This same very fast wireless networking is built in to all Time Capsules, and all currently sold AirPort Extreme routers, so there is no excuse for buying lesser equipment. The AirPort Extreme used in the demonstration was an older model, with a slower Ethernet switch and the slower 82.11g wireless networking, but that doesn’t change the advice: buy the current technology.
In setting up any network, including a wireless network, you should always start by plugging in everything using Ethernet cables. Why? It is easier to see if the cables are plugged in, it is easier to see where mistakes are made, and it generally has fewer causes for confusion or failure than wireless networking. So even if you want a purely wireless network in your home or office, invest in a couple of Ethernet cables; they are inexpensive, but invaluable during setup, or during troubleshooting.
Accordingly, Ethernet cables were strung from the Mac Pro laptop to the AirPort Extreme switch, and from the iBook G4 to the AirPort Extreme switch. The MacBook Pro was booted, and as the audience watched, file sharing was enabled (System Preferences > Sharing > File Sharing checked). At that point the MacBook was left alone, with the screen facing the audience but otherwise untouched.
Before proceeding, there was a brief discussion of computer security. If your name is Michelle Obama, and you have a MacBook Pro, and you set up your account on the MacBook using the defaults, the MacBook will give itself the network name of “Michelle Obama’s MacBook.” This is not a good idea, since the name is broadcast across the network, providing any lurking hacker with more than enough information to target the machine. Instead, go into System Preferences > Sharing, and give the computer a non-descriptive one-word name. The MacBook in the demo was named “Twintel,” and the iBook G4 was named “Fubuki.” Neither name revealed anything about the machine’s purpose or the machine’s owner.
In both cases, the hard drives were also given the same one-word name. Apple’s Disk Utility routinely names hard drives as “Macintosh HD,” which is not terribly individual and also gives potential hackers too much information. Make life difficult for them, and give the drive a different, preferably one-word name. You can find more on security in a three-part Journal series from 2005, “Mac Security: Physical, Mental and Spiritual,”
http://www.wap.org/journal/security/
One thing not mentioned in the series: if all your computers are named “Michelle” and all have hard drives named “Macintosh HD,” it is very difficult for you – or the Macs – to keep track of which machine is which. So don’t accept the default names, and don’t name your computer something obviously identifiable with you or the computer’s function (i.e., “Bank account records” would be a bad name). Several audience members had an “aha!” moment at this point, having run into the “everything has the same name” problem before.
After everything is plugged in, one important thing to note: when is your Mac fully booted? Over the years, many Pi members have complained that networking seems disabled when they first turn on their computers. This is correct: the Mac performs a series of diagnostics when it is turned on, and, after you log in, it fires up a variety of processes. Networking is one of the last processes to load, so be patient. Until all the icons show up at the top of your Finder window, the Mac is probably still waking up.
For the demonstration, as mentioned, the MacBook had file sharing turned on. The audience was then asked: what needs to be turned on for the iBook G4 to see the MacBook? Several people suggested File Sharing needed to be enabled on the iBook, too. This is a common – and dangerous – mistake.
Unless you have a full-time file server, file sharing should only be enabled for the period of time necessary to transfer files – and then it should be turned off. File sharing places extra burdens on the machine, and opens it up to vulnerabilities. With all sharing services turned off, it is very, very difficult to break in to a Mac OS X-based computer, so only turn on such services as needed.
More specific to this point: file sharing needs to be enabled on only one machine to share files. The iBook can “push” files to the MacBook or “pull” files from the MacBook; there is no need to enable sharing on both computers to make this possible. Just plug the computers into the router via Ethernet cables.
Q.: What is a router?
A.: A router is an automated traffic control system, sending network messages from one location to another. Jon Thomason, Network Architect for the Pi’s telecommunications systems, suggested a railroad switchyard, the center of the transportation system that collects everything and then sends data off to appropriate destinations.
Virtually all routers enable DHCP by default. Translated into English, this means the router will assign network addresses to all devices plugged into it, automatically. Virtually all routers will automatically seek out your ISP’s information, too, though some ISPs will insist on “registering” your router before it can connect to their network. This makes configuring a home or small office network much easier.
For the demonstration at the Pi, no effort was made to attach this small network to the school’s network. Since the Macbook Pro had previously had sharing turned on, it was a simple effort to connect the iBook to the MacBook Pro and copy a file to it.
One very valuable tool for answering network connections is in the Applications> Utilities folder: Network Utility (Figure 2). The first pane, Info, will give you the address of your computer’s network connection, its speed, and its status. Other panes can perform various tests of network connectivity. Network Utility is so handy that it deserves a permanent place in your Dock.
Figure 2: Network Utility offers a wealth of tools for diagnosing network problems. Drag it into your Dock and learn how to use it.
Using Network Utility, the iBook “pinged” the MacBook Pro across the network. A ping is named after the “ping” sound made famous by World War II submarine movies, but instead of using sonar, a ping sends a network packet to the other computer’s Ethernet port, asking, “Are you there?” This is an invaluable method of checking a network.
Strictly for geeky purposes, the iBook then logged into the MacBook Pro via ssh (secure shell), using Terminal. ssh is a secure command-line terminal, allowing you to type commands directly into the Unix portion of Mac OS X. The audience could see the screen of the MacBook Pro, which was empty, but by typing this command,
open /Applications/iTunes.app
the audience saw iTunes open on the screen of the MacBook Pro, even though nobody was touching the mouse or keyboard. This was done partially to demonstrate that yes, the two machines were indeed connected via the network, and also to demonstrate the dangers of networking: clever people can do things that you may not expect or anticipate.
Reviewing the demo, the audience was asked: how many machines need to have file sharing turned on in order to share files? Most of the audience, this time, answered, “one.” Jon Thomason, however, suggested zero. By attaching a USB hard drive to an AirPort Extreme or Time Capsule, it is easier – and safer – to turn on file sharing for the attached hard drive, and leave sharing turned off on all the computers.
Q.: Are USB drives better or faster than FireWire drives?
A.: It depends on context. Since the AirPort Extreme and Time Capsule only support USB drives, you have no choice when it comes to attaching drives to these devices. The latest model MacBooks and all MacBook Air laptops only support USB drives, too. FireWire 400 drives are faster than any USB drive, and FireWire 800 drives are twice as fast as FireWire 400 drives.
Q.: I have a 50-year-old house with wire mesh in the plaster walls. Is it possible to have a wireless network?
A.: The wire mesh makes for a great Faraday cage, which does make things difficult for wireless networking. But: you can daisy chain some wireless routers, such as the Time Capsule and the AirPort Extreme. Set up one as the “main” router, and set the second one in bridge mode to extend the wireless network into other portions of the house. It may not work, depending on a number of factors, but there is an excellent chance it will work just fine.
Q.: Non-Apple wireless routers are cheaper than Apple router. Why should we get an Apple router?
A.: Cheaper does not mean comparable. A Time Capsule, for example, has the fastest wireless networking available, 802.11n; this is rare in non-Apple equipment. It has built-in gigabit Ethernet ports; this is rare in non-Apple equipment. It also has either a 500 GB or 1000 GB hard drive, and built-in support for both Time Machine (for backing up) and file sharing, plus it also supports an external USB drive and will share a USB printer. The less expensive AirPort Extreme lacks the hard drive, but shares most of the other characteristics. Plus: if you have a Mac, you will find Mac users who know how to use an AirPort or Time Capsule; they may not have a clue how to set up your Brand X wireless router.
Q.: I have problems seeing my home network when I am using a VPN (Virtual Private Network) client to reach work.
A.: This is by design. The VPN protocol is designed to extend your office network so you can use it remotely. If you can’t see it from the office, you aren’t going to be able to see it from home: you are on your office network, even if you are sitting in your living room. If you need to print something, for example, it may be easier to print it on your office printer than to print it on a printer 10 feet away.
Q.: Can you be hacked if you turn on printer sharing?
A.: Technically, yes; people have hacked Sun, Linux and Windows machines by attacking printer sharing. Realistically, no: it just isn’t as attractive a target as other things.
President Bob Jarecke intervened and cut off questioning, as the pizza was on the way and people were hungry.
Pizza disappeared rapidly at the February meeting after a strenuous session on home networking. Photo by Richard Sanderson.
Two Special Interest Group meetings — iLife and Genealogy — were planned but when the Genealogy SIG group leader called in sick, it was decided to postpone that meeting so the planned topic could be adequately covered. Pat again led the iLife SIG and the dozen or so folks in the audience got some first hand tutoring on the Faces and Places features of iPhoto ’09.
The iPhone/iPod touch Meet Up is proving to be a big hit. Lots of little, handheld Macs were being used as folks followed along with Allen Kent, who temporarily took over the group's leadership for this meeting. The members helping members session had a few takers, but that appeared to be just right as the three volunteer helpers were all actively engaged with eager learners.
This is a rescheduling of the December meeting originally planned.
The main event will be a nuts and bolts presentation on home networking. Essentials for setting up a network in your abode will be covered to include how to keep out any intruders.
A Q & A session will kick off the day. Club news will be next, followed by Kitty’s Koffee Klatch (Mmmm, doughnuts!). After the main event, we will provide more detail on the expansion of Pi electronic services.
The lunch period will feature pizza (what else!) and after that the ”members helping members” session, the iLife and genealogy SIGs and iPhone/iPod touch "meetup" will hold their respective meetings.
Agenda:
Check the Web site again closer to the meeting for any last-minute
details. See you there!
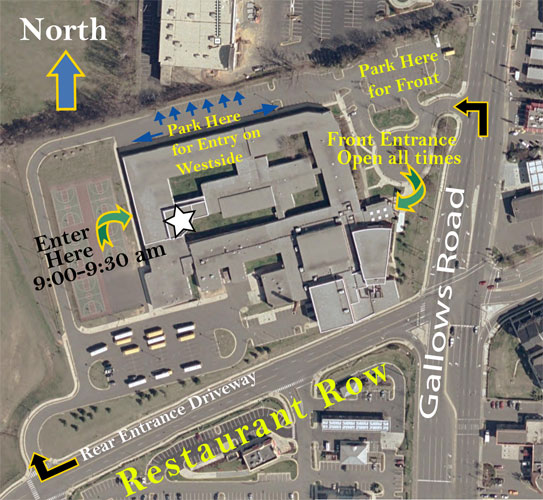
Questions: Contact the WAP office at (301) 984-0300.
The meeting, open to the public, starts at 9:30 a.m.