



Our speaker, Larry Kershberg, is Professor Emeritus of Computer Science at George Mason University, an avid photographer, and has agreat interest in Artificial Intelligence.
Complete joiurnals from the wee, dim beginnings of the microcomputer revolution.
Scenes from as far away as you can get within the U.S. from DelMarVa without a plane or a boat.
Once upon a time, Pi members typed in programs printed on computer printouts. Today members download programs from across the Internet. One thing both eras have in common: there is always more to learn, to share, and discover. Join or renew your membership as we chart a path path to the future.
Video of past meetings, plus How To videos, and testimonials. The full list is tucked away under videos.
For questions or feedback, email office@wap.org, or participate in the Apple Pi interactive email - a reminder to go here to join:
https://applepi.groups.io/g/main
A reminder that the Pi is:
Thanks for being members of the Pi!
We've posted capsule reviews of several programs designed to help you clean up clutter on your Macintosh.
Meanwhile, a photo of a mug:
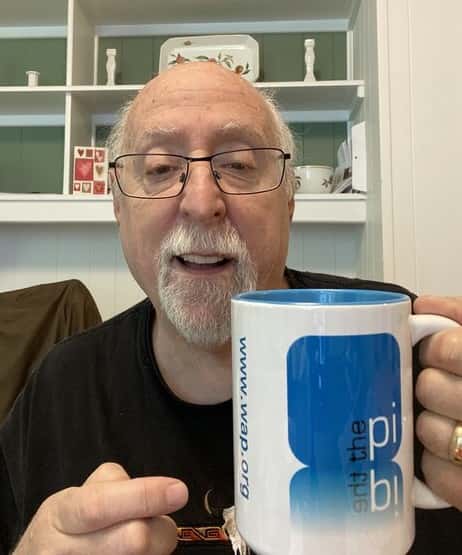
Ceramic version of Washington Apple Pi mug. A MUG (Macintosh User Group) is not normally cast in ceramic, and normally avoids water due to unfortunate side effects involving liquids, electronics, and electricity, but this mug is hydrophilic. Our highly photogenic model is former Wall Street Journal technology columnist Walt Mossberg.
A video review of the 2018 General Meeting presentations in (slightly more than) 20 minutes.
Also, check out this terrifying video on electronic mail, with our Email Compendium, Volume 1. This contains lots of snippets from the General Meeting podcasts, focusing on the subject that brought the most fear and horror to the Q&A session moderators.

⌘ Note: in case of inclement weather, Pi activities follow the closure schedule of local school districts.

Recent podcast video