



In response to the (temporary) loss of 26.5 million names and associated personally identifiable information (PII) last year, on June 23, 2006, the Executive Office of the President, Office of Management and Budget ("OMB"), issued a memorandum, M-06-16. This recommended that all executive departments and agencies encrypt all data on mobile computers and other devices unless the data was determined to be non-sensitive. Unfortunately, the OMB suggestion also suggests that the Deputy Secretary (in other words, a subcabinet political appointee) personally declare that a given device does not carry PII.
The idea of a senior political appointee personally sorting through the tens of thousands of laptops, keychain drives, external hard drives, USB mice with flash storage, and other mobile data devices, looking for PII, has a certain appeal -- matching form and function to talent and ability. Sadly, that's not going to happen; political appointees are too busy looking for more prestigious jobs.
Instead, in addition to introducing the silly looking abbreviation PII into the technical vocabulary of security professionals, the edict essentially requires that all government laptops be encrypted, as it is easier to issue blanket requirements than it is to exercise proper personnel oversight and leadership. Many cabinet agencies extended this requirement to contractor machines as well. The memorandum triggered a massive purchasing spree at the end of the federal fiscal year 2006 and the start of the fiscal year 2007, as thousands of agencies and contractors attempted to encrypt hundreds of thousands of laptops, in the process probably destroying more data than they protected.
Of course, most of this effort was focused on the Windows world, since the infamous lost laptop was running Windows and, in fact, most government laptops run Windows. Virtually all of the solutions purchased work with Windows only. So what is a Mac user supposed to do?
From the beginning, Macs really were not an issue. Mac OS X is far harder to break into than Windows, and Macs tend to be used more for creative functions (web design, Java programming, photography) and scientific purposes (gene processing, hazmat identification, astronomy) than personnel matters. And, of course, there is FileVault.
FileVault is one of those technologies that Apple built in to Mac OS X, but doesn't really talk about. It isn't as sexy as iPhoto or iTunes, or as useful as Safari or Mail. FileVault, from a user's point of view, does absolutely nothing, so it gets ignored. Yet FileVault, included with every copy of Mac OS X 10.3 and 10.4, is just the ticket for complying with the OMB M-06-16 memorandum. You don't need to go out and buy anything extra; it is right there, waiting to be used. So how do you use it?
If you are not a government laptop user, or a user of a government contractor laptop, you problably don't need to read the rest of this article. Encryption, you see, is inherently bad. Stated another way, "encryption" means "scramble your data." What you strive to save to your hard drive and protect from scrambling is secondary when you encrypt things; encryption strives to deliberately scramble what is saved to the hard drive. The trick, of course, is scrambling it in such a way that you can unscramble it.
Unless you do something silly, such as do your taxes on a laptop (a prime opportunity for identity theft if there ever was one), do not encrypt a Mac laptop. Password protect it with non-trivial passwords, do security updates, and take all the normal and standard security measures, but don't encrypt the laptop. Don't put personal or difficult to recover information on a laptop, either; compared to desktop machines, laptops are too fragile, too theftable, too likely to disappear. Stick personal, sensitive, or unique data on desktop computers, and use laptops as portable extensions of a desktop workstation.
Encryption inherently makes life more difficult. Looking specifically at encryption on a Mac:
In short, don't encrypt a latop unless you must. You are far better off storing sensitive information anywhere but a laptop. This is what OMB should have recommended. But it didn't.
Now, getting back to the government's encryption effort...
Start with Mac OS X 10.4. While FileVault is included in Mac OS X 10.3, it is recommended that you upgrade to Mac OS X 10.4 before encrypting anything. There is extensive anecdotal evidence that FileVault is more stable and dependable under Mac OS X 10.4, so use that as your starting point. You should also ensure that Mac OS X 10.4 is fully updated; keep on making trips to System Preferences > Software Updates and installing updates until nothing more is offered.
Start with a healthy disk drive. You also need to ensure that your hard drive is in good working order. Launch Disk Utility (in the Utilities folder) and use the Disk First Aid tab to Verify the hard drive. If any problems are found, correct them; don't even think about trying to encrypt a hard drive that has errors.
This is bad. Encryption essentially scrambles everything in an organized manner, and if your disk is already scrambled in a disorganized manner, don’t even think of encrypting your drive; repair the disk first.
This is good. If Disk First Aid doesn't give your drive a spotless clean bill of health, do not even think of encrypting anything.
Start with adequate room on the drive. From the Finder, select your user directory (it looks like a house, and is named with your log-in name). From the Finder menu, select Get Info. A window will appear that shows, among other things, the size of the directory. Depending on the amount of information the user has on the computer, this could take several minutes; the phrase "calculating size" will appear while the computer is conducting inventory. Then, from any Finder window, note the available space left on the drive. If you don't have twice as much free space as space used by your user directory, you won't be able to encrypt your disk; you will need to archive data to free up space.
Remove miscellaneous files. FileVault encrypts everything, even garbage, so it is a good idea to get rid of various cache files first.
Make sure the computer is plugged into power and can be left alone for an extended period of time. Encryption can take minutes or hours, depending on a number of factors.
Log into the computer, select System Preferences, and select Security.
Mac OS X 10.4 Security preference pane.
Set the Master Password. The Master Password should be a lengthy (at least 12 characters) password that you never use for any other purpose. Once you've entered it, write it down on a piece of paper, seal it in an envelope, and put it in a safe or other secure area. The Master Password is used for recovery of your encrypted information in case you ever manage to forget your log-in password.
Turn on FileVault. You will be prompted for your normal user password (not the Master Password).
FileVault will display a warning that it is about to be turned on. Note the checkbox for Secure Erase. Check this box if the computer has sensitive data that must be erased; otherwise leave it unchecked. By checking this box, the encryption process will be extended by least eight times the normal span of time.
Caption: Make sure you read and understand everything in the warning prompt before turning on FileVault. Otherwise, this will be the last time you ever see anything on your computer.
If you did not properly calculate the amount of space required, FileVault will stop and ask you to free up space.
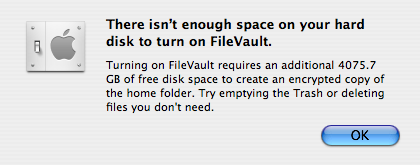
FileVault will complain if there is not enough space. Note the rather fanciful calculation of requiring another 4 terabytes of space; in reality, this laptop needed another five gigabytes of space.
Once encryption is started, a progress bar is displayed along with an estimate of the time the process might take.
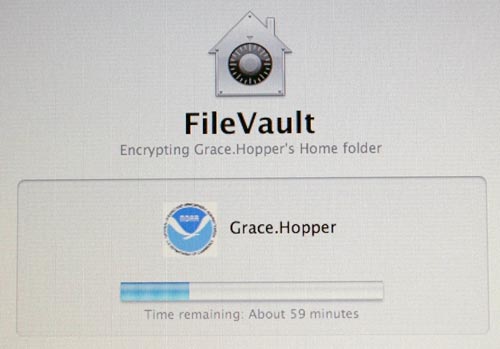
Progress bar showing estimated time remaining to encrypt the user directory. The laptop must be plugged in with adequate power for the entire process; a loss of power would be Very Bad.
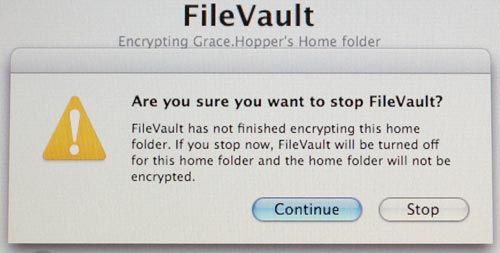
If you accidentally touch a key, you might stop the process, which will delay the job. Make sure the machine can be left alone, plugged into power, for several hours (in some cases).
Once the encryption process is finished, the machine will be left at a login screen. Have the user log into the machine and confirm it is encrypted. The login process will take a few extra seconds (as will logout) once the machine is encrypted.
Aside from taking slightly longer to log in and out, using a Mac with FileVault is transparent; a user is unlikely to notice a difference. One exception to this rule: video editing. If you use a laptop for video capture, you may have trouble saving a video stream to an encrypted disk drive.
If the user deletes a large volume of information, they may see an offer that FileVault can reclaim the extra space. Be sure and answer this question, and do not interfere with the process; killing power instead of answering the question can be bad. Very bad.
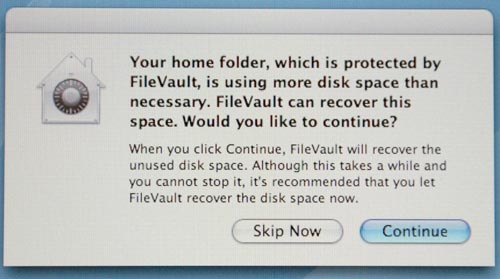
If you see this question, answer it. Don't try and kill the power or something similarly silly, or you may never see your data again.